| University | University of Wollongong (UOW) |
| Subject | CSCI368 Network Security Assignment |
CSCI368 Network Security Assignment, UOW, Singapore: Consider the following key exchange protocol which is a variant of the Diffie-Hellman protocol
1. Consider the following key exchange protocol which is a variant of the Diffie-Hellman protocol. Each user P has a secret key sk_P=x_P and public key pk= gx_P mod p.
1: A B: gr_A mod p
2: B A: gr_B mod p
In the protocol, r_A and r_B are randomly chosen in each session by A and B. The shared key for communication is defined as K = gr_Ax_B + gr_Bx_A mod p.
a) Show the key derivation formulas of User A and User B (i.e., how does each
user compute the shared key?)
c) Does the protocol provide Forward Secrecy? Justify your answer.
Hire a Professional Essay & Assignment Writer for completing your Academic Assessments
2. Two questions related to the A1. For each question, you should use one sentence to highly summarize the problem (1 mark) and then use 1-3 sentences to explain it.
a)Briefly describe the issue when the adversary is able to know the secret key sk_s.
b)Briefly describe the problem when Alice’s algorithm always uses the same r for secure communications. (2 marks)
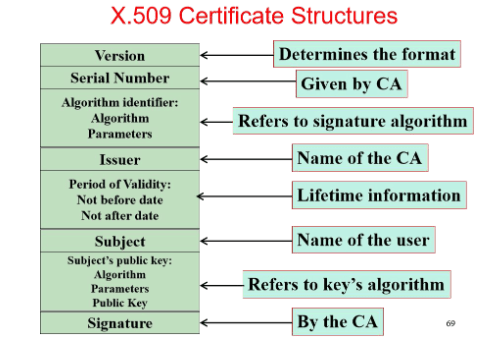
The CA generates the signature but the message to be signed excludes “Refer to Key’s Algorithm”. Describe how the adversary can launch the MITM attack on TLS protocol in the real world. You should start with the application scenario that user Alice wants to access the web resources manager by the web server Bob. You should use at least three steps to highly describe this kind of attack.
Buy Custom Answer of This Assessment & Raise Your Grades
Need Singapore assignment help review or assistance with CSCI368 Network Security Assignment? Look no further. Our Dissertation Writing Services cater to Singaporean students seeking expert guidance. From comprehensive reviews to tailored assignments, our experts ensure top-notch support for your academic success.
Tags:-
- Imagine that you are currently working for a precision medicine startup: Machine Learning Paper Review in Precision Medicine, Written Assignment 1, NUS, Singapore
- Go Business offers PSG solutions for enterprises in Singapore: Collective Intelligence and Entrepreneurship, Assignment 1, JCU, Singapore
- Design an ontology based on- Accidents can be categorised as chemical, electrical, fire, kinetic or liquid: Collective Intelligence and Entrepreneurship, Assignment 1, JCU, Singapore
- Project Control Monitoring, Assignment, HU, Singapore: Deliberate Project MONITORING AND CONTROL or PMC Identification
- DSM500: Final Project Report, Coursework 2, UOL, Singapore
- DSM080: Financial Markets, Assignment, UOL, Singapore: A grapefruit juice futures contract is for 15,000 pounds of frozen grapefruit juice
- DSM080: Financial Markets, Assignment, UOL, Singapore: The share price of a certain stock today is $42.50, and five-month European style call options with a strike price of $45 currently sell for $4.25.
- DSM080: Financial Markets, Assignment, UOL, Singapore: A trader who is working in the gold markets is able to borrow money at the interest rate of 7% per annum
- DSM080 Financial Markets, Assignment, UOL, Singapore: A dollar-based American corporation has decided that it will have to pay 6 million UK pounds in three months
- Principle of Finance Assignment, UCD, Singapore: National Gaming Inc. (National) operates the weekly lottery in the country
UP TO 15 % DISCOUNT